Exclusive Interview:
Anonymous Sudan, Cyber Warriors or Russian Puppets?

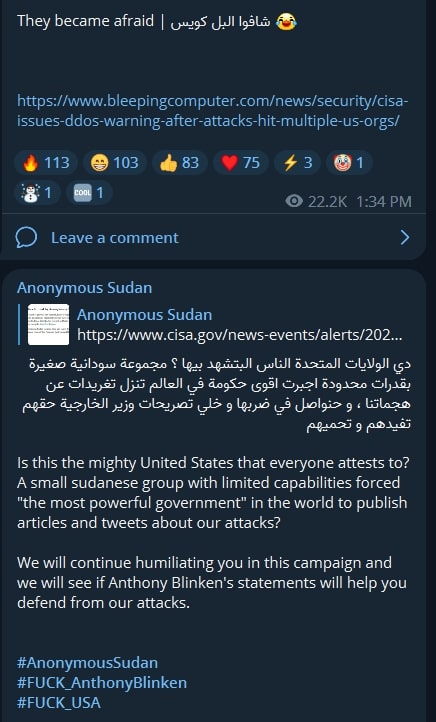
In the fast-paced world of the cyber underground, Russia-linked Anonymous Sudan has emerged as a formidable attacker, claiming responsibility for a staggering 63% of the total identified DDoS attacks attributed to the pro-Russian KillNet collective in 2023 (Mandiant). Of particular interest is their focus on targeting US and European organizations, which has generated both intrigue and skepticism regarding their true intentions and identity.
In late June, I established contact with Anonymous Sudan and embarked on a two-and-a-half-week exchange, hoping to shed some ligt on their operations and motivations. Traditionally circumspect, they accepted to be interviewed by Intel Cocktail provided I am paired with a media organization or personality with a large audience base to promote public notoriety. I conducted the interview with Joe Tidy of the BBC through Telegram.

Despite Anonymous Sudan’s brevity and shrewdness in handling our questions, instructive revelations are gleaned into their motives.
The intrigue began immediately. At first, their representative “Crush” appeared relaxed about the interview start and duration, yet hours later, he expressed urgency, stating: “I hope you can hurry up with the questions because the internet could be cut off at any moment.” Presumably, this was a ploy to deflect their Russian identity, part of their pretext portraying themselves as Sudanese cyber warriors currently facing instability in their country. As our conversation unfolded, it became clear that the group taking down US government, Mossad, and Microsoft websites experienced no such disruptions.
During my initial contact with the group, communication was exclusively in Sudanese Arabic. After we sent the first set of questions, Crush asked whether we preferred to receive the answers in Modern Standard Arabic (MSA) or the Sudanese dialect. Communicating that either option was fine, Crush promised a response in a few minutes which turned into hours, a common theme throughout the interview. Crush often acknowledged receipt of questions promptly but took hours or days to reply, depending on how inquisitive our questions were, possibly indicating consultation with a larger team. Also, he answered all questions in fairly good English, which is curious, considering his earlier question.
When questioned about the group’s identity and affiliation with the international hacktivist collective ‘Anonymous,’ Crush clarified: “We name ourselves Anonymous Sudan simply because we are all from Sudan. We do not have any links to Anonymous.”
Their long-term goals are ambitious, centered around showcasing the capabilities of the Sudanese people, stating with conviction that “Sudanese people, although with limited capabilities, have very good skills in many different fields. We made the group to defend the Truth, Islam, Sudan, and any matter we see that aligns with the Truth by attacking anyone who goes against those 4 matters.”
According to cybersecurity solutions provider Radware, attacks carried out by Anonymous Sudan originate from tens of thousands of unique IP addresses, with UDP traffic reaching an immense 600 Gbps. On April 30th, an official post in Anonymous Sudan’s Telegram channel claimed that they could execute application layer 7 attacks with “35 Million Requests Per Second,” along with transport layer 4 attacks involving “4 TB UDP” and “1.7 TB SYN” traffic.

When asked about financing their attacks, Crush stated that their priority lies in technical skills rather than funding, explaining: “Financing our attacks is not a priority. Having the necessary skills is more than enough. Financing will only help us to increase the effect of our attacks, but we have the necessary skills to work with what we have.”
“All operations are studied, and we have a plan to follow. As for the infrastructure, it depends on the target,” they blandly stated when asked to explain their operations. They emphasized the collective nature of their group when asked about their group’s composition and dynamics, stating: “Our geographical locations are not important. The most important thing is that we are all Sudanese. We communicate with each other on a daily basis, and as for coordination, it depends on what happens in the world. For example, when Israel strikes Palestine, we will change our target and focus on Israel in order to support Palestine with what we can.”
When asked to describe their tactics, techniques, and procedures (TTPs) in detail, Crush deflected: “It depends on the target, if it requires an L4 attack we do that, if it requires an L7 attack we do that. And if it requires other forms of attacks, we do that too.”
Regarding the development of botnets and other exploits, Anonymous Sudan revealed that they do not outsource attacks to third parties, but still provided little detail to understand their methods from a technical point of view, adding: “We develop our own methods of attacks, and we update them weekly if needed. For example, if a company we are targeting upgraded their protection, we update our attacks similarly to be able to attack this target properly,” Crush shared, indicating inordinate technical capabilities and agility.
Addressing the accusations of being part of a Russian cyber military campaign, Anonymous Sudan vehemently denied any such association: “Those claims are all baseless and false, we sometimes write in Russian simply because there are many Russian members in our channel,” they asserted.
The group’s animosity towards US Secretary of State Anthony Blinken – included in their numerous claims of attack against US websites – was explained as: “Anthony Blinken wants to meddle in Sudanese affairs, and we will attack any foreign country that tries to meddle in our internal affairs.”

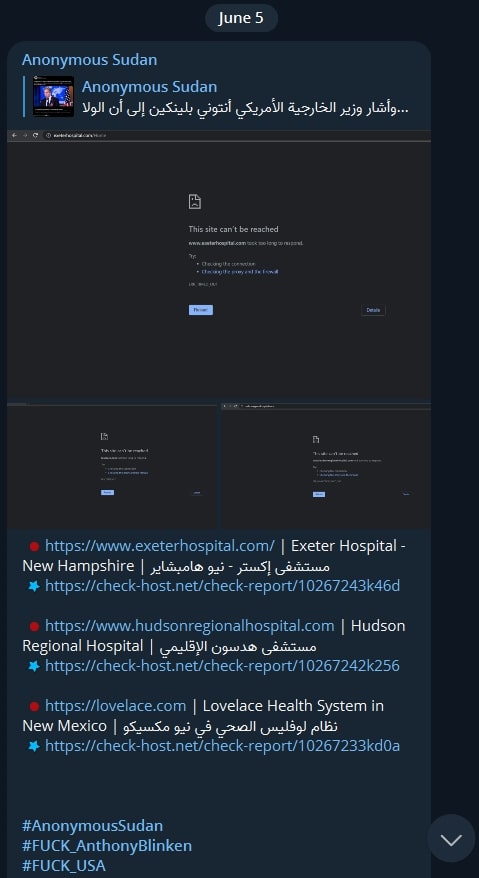
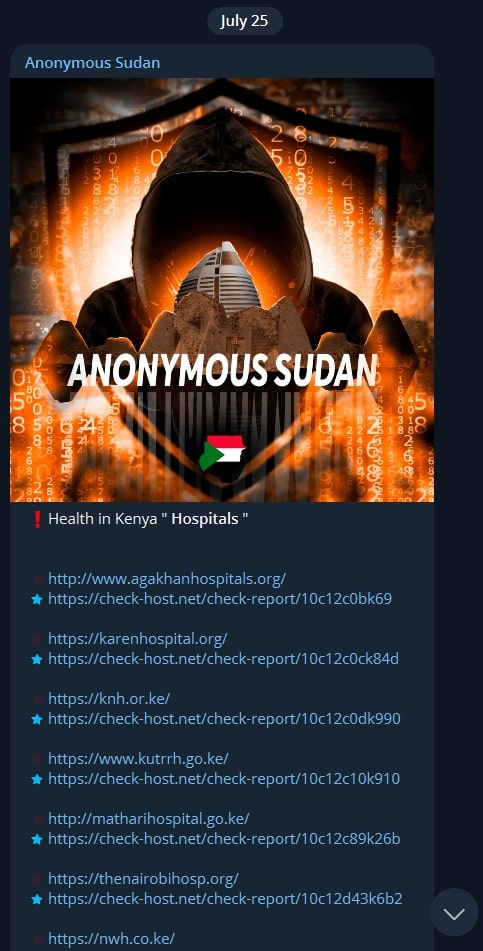
We confronted Anonymous Sudan about their indiscriminate targeting of critical infrastructure, which defies typical black hat ‘etiquette.’ They defended their actions, stating: “The reason we hit infrastructure is to teach the country and its rulers a lesson, and yes we have red lines, that is if our attacks harm a lot of innocents.” But as we all know, taking down American, Australian, Danish, French, Israeli, Kenyan, and Israeli hospital websites – which the group has previously done – could already “harm a lot of innocents.”
We shifted the conversation by asking two probing questions together:
- “You have previously called Zelenskyy a hypocrite. What does your group think of Vladimir Putin?”
- “As self-proclaimed religious hackers that defend Islam and attack anyone in the way of Islam, you have never criticized, for example, indiscriminate Russian bombing in Syria like last week’s random airstrike on a vegetable market which killed innocent civilians. Do you condemn such attacks and other Russian attacks on Muslim civilians in Syria?”
In response, they vaguely stated: “We do not personally support Putin. We stand with what is right only. This logic can be used to answer both questions.” Pressing the issue further, we asked again if they condemned Russian bombing of innocent Muslim civilians in Syria. This time, hours after receiving read receipts to this question, they interestingly responded: “Of course we condemn it, this shouldn’t be questioned.” As religious Muslim hacktivists, why were they initially evasive and did not condemn all attacks from the first time?


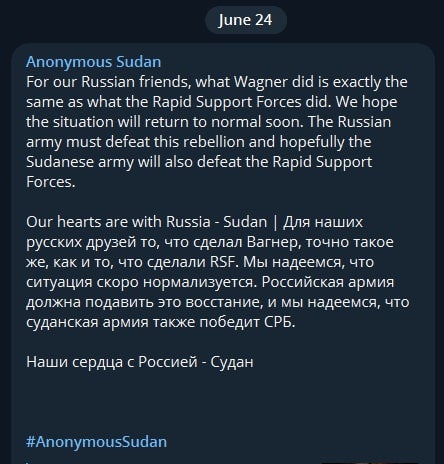
During the interview, the Wagner insurrection unfolded, and Anonymous Sudan declared support to the Kremlin. Via their official Telegram channel, the group stated: “The Russian army must defeat this rebellion,” and: “Our hearts are with Russia”. We asked them why a Muslim Sudanese group was so involved in Russian affairs. Crush replied: “We don’t care or focus on Russian affairs, but a similar thing happened to our country, and Russians stood with us, so we wanted to pay them back.”
Certainly, an unexpected stance supporting the same Russia that had just bombed civilians in Syria!
We also pressed the self-proclaimed defenders of Islam on their lack of attacks against China for its mistreatment of 1 million Muslim Uyghurs, and it became clear that Anonymous Sudan’s handlers reached their (very low) threshold of acceptable probing. Crush promptly ended the interview, stating “We think the questions and answers already given are sufficient. We will not answer any new questions. I believe this is enough as there are questions that are being repeated and we have already answered them, but you want a specific answer and I understand that.”
Could Anonymous Sudan indeed be skilled Sudanese cyber warriors amid internal strife in Sudan, or is this an ongoing clever Russian operation designed to maintain plausible deniability as defenders of Islam while striking at the West? The evidence seems to point towards the latter, while the real identity and details of this elusive group remain shrouded in darkness.
